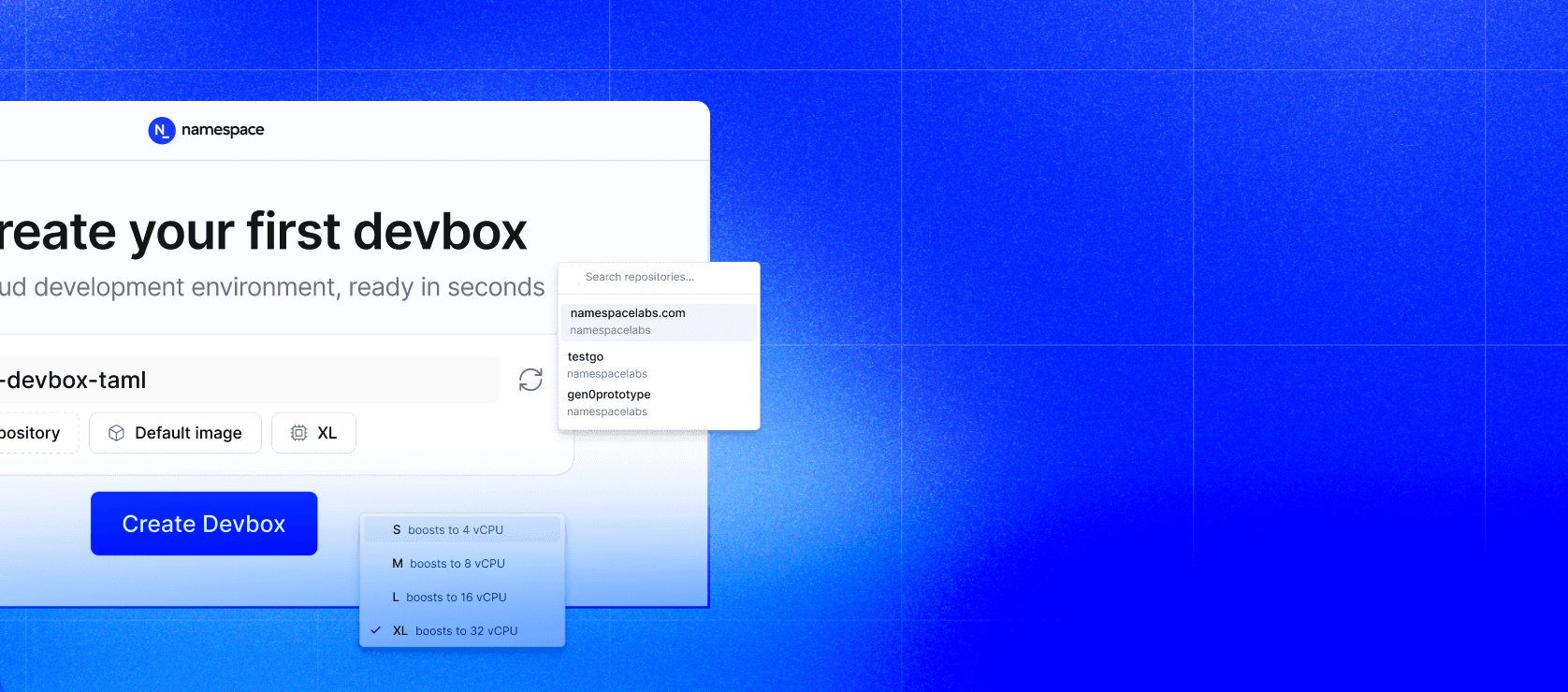
Introducing Devboxes
Read article
We're hiring, Join us!
Open rolesSandboxes
Build your own sandbox
for any workload
Start with Namespace compute as the foundation. Layer on Dockerfiles, network policies, storage, and APIs to create the exact sandbox your agents and workloads need.
Start with fast, isolated compute
Every sandbox starts as a Namespace compute instance, a microVM with a dedicated kernel, filesystem, and network stack. No shared runtimes, no container escapes, no noisy neighbors. From there, you customize it to your needs.
Fast boot times
Our compute instance boot up quickly so your agents and workloads starting running almost instantly. Our infrastructure is designed and built for code-based workflows.
Learn about our architecture →Isolation by default
Every sandbox runs in its own microVM. This isn't container isolation, it's a virtual machine with a dedicated kernel. Run untrusted code with confidence.
Customize everything
Layer Namespace features on top of compute to build the exact sandbox environment your workload needs. Every aspect is configurable.
Dockerfile-based images
Define your sandbox environment with standard Dockerfiles. Pre-install languages, tools, and dependencies. Every sandbox boots into a known-good state.
Network policies
Control exactly what your sandbox can reach. Allow specific egress, block everything else, or create fully air-gapped environments.
Persistent & ephemeral storage
Attach volumes for state that persists across sessions, or use fully ephemeral storage that's destroyed with the sandbox.
SSH & exec access
Connect to sandboxes via SSH or execute commands programmatically. Give agents direct terminal access to build, test, and iterate.
Snapshots & cloning
Snapshot a sandbox at any point and clone it to create identical environments instantly. Perfect for branching agent workflows.
Ingress & port forwarding
Expose services running inside sandboxes to the internet. Preview web apps, serve APIs, or connect external tools.
Define it with a Dockerfile
Use standard Dockerfiles to define your sandbox environment. Install tools, configure runtimes, and set up everything your workload needs.
1 Familiar tooling, complete control
Use any base image. Install any package. Configure any runtime. Your Dockerfile defines a reproducible sandbox environment that boots the same way every time.
Images are cached and deduplicated, so even complex environments boot in seconds.
Orchestrate with code
Use Go and TypeScript SDKs to create, configure, and tear down sandboxes programmatically. Build sandbox orchestration into your agent framework or platform.
Full lifecycle control
Create a sandbox, run commands, read outputs, and destroy it. The SDK handles authentication,connection management, and cleanup.
Build agent loops that spin up sandboxes on demand, execute code, verify results, and tear everything down automatically.
Explore the SDK →1 Built for builders
Use Namespace sandboxes to power a wide range of workloads anywhere you need. Fast, isolated, and programmable compute.
AI coding agents
Give each agent its own isolated environment to write, build, and test code with full root access and no risk of cross-contamination.
Code execution platforms
Run untrusted user code safely inside disposable microVMs. Each execution gets a fresh environment with VM-level isolation.
Preview environments
Spin up a full-stack environment for every pull request. Give reviewers a live, isolated preview that matches production.
Security testing
Run fuzz tests, pen tests, and vulnerability scans in fully isolated sandboxes. No risk to your production infrastructure.
Built for Enterprise
Built with security and robust-first principles, Namespace supports large, fast-paced organizations, with unique requirements.
Flexible billing and enterprise-grade fine grained access controls.

Transactional audit logging, with SIEM integration.

Network observability & enforcement: performance and security insights, job-wide network policies to constrain egress.










Build your sandbox today
Start with Namespace compute and customize it to build the exact sandbox your workloads need.